Category: Executive Protection
-

Free Webinar by Mellon360 – From Connections to Contracts
Do you want to learn how to market yourself properly in the security industry and go from Connections to Contracts? Mellon360° Marketing For Security is hosting a FREE 3-hour webinar on a topic that’s often overlooked—or misused—in our industry: Marketing for Security Professionals
-

CEOs Under Attack – The Growing Risks for Corporate Leaders
This article was first published in Chief Executive Officer The recent assassination of UnitedHealthcare CEO Brian Thompson has cast a spotlight on the vulnerabilities faced by many corporate leaders and is a great example of how C-Suite executive’s safety can affect not only their personal wellbeing, but also can drastically affect a company’s reputation and…
· Aggression Management, Athena Bodyguards, Bodyguard Careers, Bodyguard Lessons, Bodyguards in USA, British Female Bodyguards, Celebrity Bodyguards, Conflict Management, Conflict Resolution, Corporate Security, Counter Surveillance, Executive Protection, Executive Protection Companies, Female Bodyguards, female close protection operatives, hire a bodyguard, threat assessment, vulnerability assessment, workplace violence prevention -
Operational Communication for Close Protection Operations
In the world of security operations, one of the most critical areas is communication, which involves constant cooperation and vital information sharing between top-level executives, their respective EA/P/A, the GSOC team, company employees, vendors, and agents working on the ground. Now, if you have been working for any reasonable amount of time in our industry, we…
· ATHENA Worldwide Categories, Bodyguards in USA, British Female Bodyguards, Celebrity Bodyguards, Child Protection, Child Protection Specialist, Close Protection Training, Conflict Management, Contract Management, Corporate Security, Dignitary Protection, Diplomatic Protection, Event Security, Executive Protection, Executive Protection Companies, Executive Protection Training, family protection, female bodyguard careers, marketing for security, Protective Intelligence, residential security, Risk Assessment, security companies, security family offices, Security for Royal Family, Security Industry Standards, security manager, threat assessment, travel logistics, travel security, UK bodyguards -
How to eliminate some ”new guy” mistakes in EP (certificates, association memberships, licenses)
Even though I addressed this subject over twelve years ago, the same still rings true. In the world of executive protection/close protection, there are already so many distractions, pitfalls, and misunderstandings that I believe there is a veritable need to, again, address the distinction and perceived necessity surrounding certifications, licenses, and memberships/associations that so many…
· Bodyguard Careers, Bodyguard Lessons, Bodyguard Training, Bodyguards in USA, Celebrity Bodyguards, Child Protection Specialist, Close Protection Courses, Close Protection Training, Corporate Security, Dignitary Protection, Diplomatic Protection, Executive Protection, Executive Protection Companies, Executive Protection Course, Executive Protection Training, female bodyguard careers, female close protection operatives, female executive protection, security associations, security certificates, security companies, Security Industry Standards, security manager, security vetting -
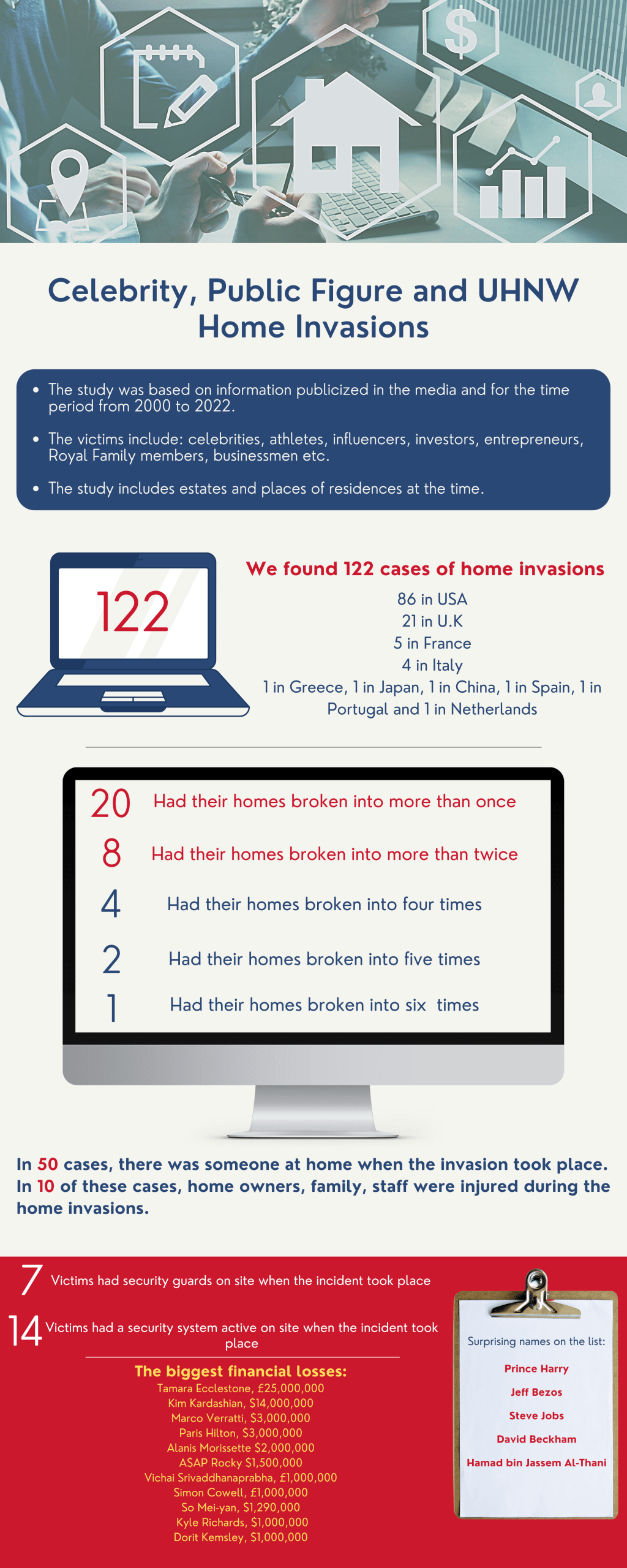
Residential Security-It is more important than you think
What do celebrities like Piers Morgan, Tyler Perry, Paris Hilton, Simon Cowell, Ariana Grande, Kate Moss, Kim Kardashian, Rita Ora, Rihanna, Hilary Duff, Lindsay Lohan, Dorit Kemsley, Bella Thorn, Kelly McGillis, Chris Brown, Miley Cyrus, Kanye West… (Yeah, the list is a bit long, isn’t it? Wait though, we’re not done yet…), Sandra Bullock, Selena…